Академический Документы
Профессиональный Документы
Культура Документы
LESSON 15 The Disadvantages of ICT
Загружено:
Niko Gozun100%(2)100% нашли этот документ полезным (2 голоса)
1K просмотров22 страницыThe document discusses cybercrimes and methods for combating them. It lists 10 common cybercrimes, including phishing, blackmail, hacking, illegal gambling, fraud, harassment, child pornography, drug trafficking, and copyright infringement. It then describes three methods for combating cybercrimes: network security measures, investigation through IP address tracing, and penalties under developing cybercrime laws. Key terms related to cybercrimes are also defined. Students are assigned seatwork questions about new cybercrimes, copyright law implementation, and how ICT could benefit their future careers.
Исходное описание:
informations about the disadvantages of ict
Оригинальное название
LESSON 15 the Disadvantages of ICT
Авторское право
© © All Rights Reserved
Доступные форматы
PPTX, PDF, TXT или читайте онлайн в Scribd
Поделиться этим документом
Поделиться или встроить документ
Этот документ был вам полезен?
Это неприемлемый материал?
Пожаловаться на этот документThe document discusses cybercrimes and methods for combating them. It lists 10 common cybercrimes, including phishing, blackmail, hacking, illegal gambling, fraud, harassment, child pornography, drug trafficking, and copyright infringement. It then describes three methods for combating cybercrimes: network security measures, investigation through IP address tracing, and penalties under developing cybercrime laws. Key terms related to cybercrimes are also defined. Students are assigned seatwork questions about new cybercrimes, copyright law implementation, and how ICT could benefit their future careers.
Авторское право:
© All Rights Reserved
Доступные форматы
Скачайте в формате PPTX, PDF, TXT или читайте онлайн в Scribd
100%(2)100% нашли этот документ полезным (2 голоса)
1K просмотров22 страницыLESSON 15 The Disadvantages of ICT
Загружено:
Niko GozunThe document discusses cybercrimes and methods for combating them. It lists 10 common cybercrimes, including phishing, blackmail, hacking, illegal gambling, fraud, harassment, child pornography, drug trafficking, and copyright infringement. It then describes three methods for combating cybercrimes: network security measures, investigation through IP address tracing, and penalties under developing cybercrime laws. Key terms related to cybercrimes are also defined. Students are assigned seatwork questions about new cybercrimes, copyright law implementation, and how ICT could benefit their future careers.
Авторское право:
© All Rights Reserved
Доступные форматы
Скачайте в формате PPTX, PDF, TXT или читайте онлайн в Scribd
Вы находитесь на странице: 1из 22
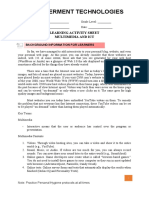
Lesson 15
The Disadvantages of ICT
Cybercrimes
• Cybercrimes are illegal acts done
through the use of the Internet.
In 2012, Stephen Nale (Complex.com)
posted a list of ten most common
Internet cybercrimes as follows:
1. Phishing/Spoofing
– the act of sending multiple
emails to multiple users in hopes
of having a number of them
clicking on the links or malwares
attached to the email.
2. Blackmail/Extortion
– the act of using the Internet to
threaten or damage someone’s
reputation to extort money or
anything else of value. This can be
avoided if you are aware of what
you should post on the Internet.
3. Accessing Stored Communications
– or hacking; the act of obtaining
unauthorized access to data from
a computer network.
4. Sports Betting
– the act of wagering on any sports
event over the Internet. In some
countries, gambling (including sports
betting) is illegal even if you are
doing it over the Internet.
5. Non-Delivery of Merchandise
– the act of devising a scheme
wherein a culprit posts an item or
service for sale over the Internet and
once the transactions have been
done, does not really give the item or
service.
6. Electronic Harassment
– the act of anonymously using
the Internet to harass, abuse,
threaten, or annoy other people.
7. Child Pornography
– the act of using the Internet to
show child pornography. This act
is highly punishable by law.
8. Drug Trafficking
– the act of selling illegal
substances using the Internet.
9. Criminal Copyright Infringement
– the act of piracy mainly for financial gain.
In late 2014, the number one pirate website,
ThePirateBay, was raided for the second
time due to years of pirating movies, music,
games, books, and other software. These
kinds of websites earn money through
advertising.
Combatting Cybercrimes
1. Network Security. Before a hacker
can get through the unauthorized files
he or she is targeting, the hacker has to
get through several security measures
like firewalls, secure connections,
passwords, anti-malwares, and data
encryptions.
Combatting Cybercrimes
2. Investigation. URL tracing and
logging are used by websites to track
your unique IP addresses. This can be
used by investigators to trace hackers.
In piracy, trackers are used to identify
IP addresses currently sharing a pirated
file.
Combatting Cybercrimes
3. Penalties. More and more
laws are being created and
implemented today. Penalties
include both a fine and
imprisonment.
Key Terms
• Phishing – also referred to as spoofing;
an act of spamming e-mails
• Spam – unwanted emails
• Blackmail – act of asking something
in return of not showing something
that could damage someone’s
reputation
Key Terms
• Hacking – the act of obtaining
authorized information
• Cyberbullying – an act of
harassment using electronic means
• Copyright infringement – an act of
piracy mainly for financial gain
Key Terms
• Encryption – the process of
converting raw data into code
SEATWORK:
1. What are other cybercrimes that
were not discussed in this lesson that
you think students of your
generation should be aware of?
Why?
SEATWORK:
2. Are the laws on copyright being
implemented in the Philippines?
Defend your answer.
SEATWORK:
3. As a future professional in your
respective field, what are the
things that you think ICT can do
to help you in your field?
Performance Task:
• Make an advertisement (slogan) to
campaign on fight against
cybercrime. (20 pts.)
• *OSLO PAPER
Вам также может понравиться
- Repair Manual For Claas Mega 202 218 Combine HarvesterДокумент382 страницыRepair Manual For Claas Mega 202 218 Combine Harvesterramunas100% (7)
- Fire Alarm Sys Nec 760Документ10 страницFire Alarm Sys Nec 760nadeem Uddin100% (1)
- ICT Project For Social Change 1Документ45 страницICT Project For Social Change 1Ritz Santiago100% (1)
- EMPOWERMENT TECHNOLOGY Lesson 1 - Introduction To Empowerment TechnologyДокумент10 страницEMPOWERMENT TECHNOLOGY Lesson 1 - Introduction To Empowerment TechnologyRioLeongson100% (2)
- ET Lesson 7 - Online Platform For ICT Content DevelopmentДокумент7 страницET Lesson 7 - Online Platform For ICT Content DevelopmentMaria Mae Peligro100% (1)
- Empowerment Technologies: Quarter 2Документ26 страницEmpowerment Technologies: Quarter 2Oreo Productions100% (2)
- Online Safety, Security, Ethics, and EtiquetteДокумент24 страницыOnline Safety, Security, Ethics, and EtiquetteSherwin SantosОценок пока нет
- L14 ICT Project MaintenanceДокумент9 страницL14 ICT Project MaintenanceRutchel Martinez100% (8)
- L15 The Disadvantages of ICT 1Документ15 страницL15 The Disadvantages of ICT 1don't mind me just a dead memeОценок пока нет
- Empowerment Technologies Lesson 2Документ40 страницEmpowerment Technologies Lesson 2Em Gongora Jr.100% (1)
- Principles of Interactivity and Rich Content in The Context of Web 2.0 and The Participation of The User in The Online ExperienceДокумент9 страницPrinciples of Interactivity and Rich Content in The Context of Web 2.0 and The Participation of The User in The Online ExperienceRene Andrei BuenОценок пока нет
- Empowering TechnologyДокумент4 страницыEmpowering Technologyella clapanoОценок пока нет
- Lesson 9: ICT As A Platform For Change: Empowerment TechnologiesДокумент21 страницаLesson 9: ICT As A Platform For Change: Empowerment TechnologiesApryl Erika TalosigОценок пока нет
- Online Safety, Security, Ethics, and NetiquetteДокумент12 страницOnline Safety, Security, Ethics, and NetiquetteanthonyОценок пока нет
- L12 ICT Project For Social ChangeДокумент7 страницL12 ICT Project For Social ChangeCamille Manalo50% (2)
- Designing and Copywriting For ICT ProjectsДокумент9 страницDesigning and Copywriting For ICT ProjectsLorenz Bello100% (1)
- Empowerment Course OutlineДокумент3 страницыEmpowerment Course OutlineCristy Balubayan NazarenoОценок пока нет
- Lesson 2 Online Safety, Security and Netiquette and Kinds of Online ThreatsДокумент8 страницLesson 2 Online Safety, Security and Netiquette and Kinds of Online Threatsjeremie mesinaОценок пока нет
- Computer Addiction Power Point PresentationДокумент24 страницыComputer Addiction Power Point PresentationGee A50% (4)
- Empowerment Technologies Lesson 1Документ21 страницаEmpowerment Technologies Lesson 1Bryan Aguila Bautista100% (2)
- 2 Online Safety, Security, Ethics, and EtiquetteДокумент73 страницы2 Online Safety, Security, Ethics, and EtiquetteVerna VillavicenteОценок пока нет
- Empowerment Technologies: Quarter 2 - Module 6: Multimedia and ICTДокумент16 страницEmpowerment Technologies: Quarter 2 - Module 6: Multimedia and ICTEarl Lawrence Lacubtan0% (1)
- E-Tech - Lesson 2Документ30 страницE-Tech - Lesson 2Jennifer Dela Cruz Fortu100% (1)
- Information Communication Technology: Social Relationships and Political MovementsДокумент16 страницInformation Communication Technology: Social Relationships and Political MovementsHanessyОценок пока нет
- MIL - Quarter 3 - Module 4Документ7 страницMIL - Quarter 3 - Module 4Darlene Dacanay David100% (1)
- EMPOWERMENT TECHNOLOGY - TQ (1st Quarter 2023)Документ2 страницыEMPOWERMENT TECHNOLOGY - TQ (1st Quarter 2023)Louie Jane EleccionОценок пока нет
- Lesson 14 Ict Project MaintenaceДокумент23 страницыLesson 14 Ict Project MaintenaceKatherine Joy Zaldivar Mangaoang100% (1)
- Empowerment Technology (COT 3)Документ17 страницEmpowerment Technology (COT 3)Anna Marie Carmen Cervantes100% (1)
- ETECH 2nd QuarterДокумент39 страницETECH 2nd QuarterReynalyn Guerrero0% (1)
- Empowerment Technologies: Quarter 2 - Module 13: ICT As Platform For ChangeДокумент19 страницEmpowerment Technologies: Quarter 2 - Module 13: ICT As Platform For ChangeMarilyn EstebeОценок пока нет
- Empowerment Technologies - LAS - Week 4Документ6 страницEmpowerment Technologies - LAS - Week 4Kay Tracey UrbiztondoОценок пока нет
- Empowerment Technologies: Quarter 1 - Module 2: Online Safety, Security, Ethics, and EtiquetteДокумент12 страницEmpowerment Technologies: Quarter 1 - Module 2: Online Safety, Security, Ethics, and EtiquetteArlene FlorОценок пока нет
- Q1 Module 5 DIASSДокумент18 страницQ1 Module 5 DIASSLearniedevy MitchОценок пока нет
- Mail Merge and Label GenerationДокумент8 страницMail Merge and Label GenerationSaclangan NobelОценок пока нет
- Rich Content in The Online Environment and The User ExperienceДокумент14 страницRich Content in The Online Environment and The User ExperienceJunela CharisОценок пока нет
- Quiz #5 ChristianityДокумент1 страницаQuiz #5 ChristianityRolando Corado Rama Gomez Jr.Оценок пока нет
- Empowerment Tech 12 Week 1-2 PDFДокумент12 страницEmpowerment Tech 12 Week 1-2 PDFJames Angelo MojaresОценок пока нет
- Lesson 1 ICT-in-the-Context-of-Global-CommunicationДокумент23 страницыLesson 1 ICT-in-the-Context-of-Global-CommunicationBee Neil33% (3)
- 2 LESSON Rules of NetiquetteДокумент75 страниц2 LESSON Rules of NetiquetteCassieОценок пока нет
- Emtech Slas 4 Week 4Документ10 страницEmtech Slas 4 Week 4Harold Nalla HusayanОценок пока нет
- Cyberbullying, Digital Divide and Internet AddictionДокумент34 страницыCyberbullying, Digital Divide and Internet AddictionJohn Rimzart NietesОценок пока нет
- Emptech - Week3 (Mail Merge)Документ15 страницEmptech - Week3 (Mail Merge)Al Lhea Bandayanon MoralesОценок пока нет
- People Media: Media and Information LiteracyДокумент33 страницыPeople Media: Media and Information LiteracyJames Albert S. PoleroОценок пока нет
- Grade 12 Etech TVL q2wk8Документ14 страницGrade 12 Etech TVL q2wk8VERDADERO LevisthoneОценок пока нет
- Week 1 Lesson Plan EMP TECHДокумент2 страницыWeek 1 Lesson Plan EMP TECHCake Honey SaladОценок пока нет
- Online Safety Security Ethics EtiquetteДокумент50 страницOnline Safety Security Ethics EtiquetteChyna QuiambaoОценок пока нет
- Daily Lesson Log Empo TechДокумент5 страницDaily Lesson Log Empo TechHazel-Lynn MasangcayОценок пока нет
- LESSON 3 Applied Productivity Tools With Advance Application TechniquesДокумент6 страницLESSON 3 Applied Productivity Tools With Advance Application TechniquesCLARK KENTH C. AGULO100% (1)
- Current and Future Trends of Media and InformationДокумент11 страницCurrent and Future Trends of Media and InformationCherry Mae BarbatonОценок пока нет
- TVL Empowerment Technologies q3 m4Документ15 страницTVL Empowerment Technologies q3 m4azumi0412Оценок пока нет
- Empowerment Technologies BowДокумент4 страницыEmpowerment Technologies BowHarold Nalla HusayanОценок пока нет
- Module3 - Contexts of 21st Century Philippine Literature From The RegionsДокумент6 страницModule3 - Contexts of 21st Century Philippine Literature From The RegionsJa KeОценок пока нет
- Senior High School Empowerment Technology: Benmar E. Tubeo Author Week 3 and 4Документ14 страницSenior High School Empowerment Technology: Benmar E. Tubeo Author Week 3 and 4John Benedict Albay100% (2)
- Nfhs - SHS: Lesson 6: Assistive MediaДокумент12 страницNfhs - SHS: Lesson 6: Assistive MediaRyan TusalimОценок пока нет
- Chapter 11 ICT Project For Social ChangeДокумент4 страницыChapter 11 ICT Project For Social ChangeSyrill Cayetano100% (1)
- L12 ICT Project For Social ChangeДокумент7 страницL12 ICT Project For Social ChangeNiko Gozun100% (1)
- Objectives: at The End of This Lesson, The Students Should Be Able ToДокумент53 страницыObjectives: at The End of This Lesson, The Students Should Be Able ToJayram Javier0% (1)
- Activity Sheet Empowerment Technologies Module 1Документ3 страницыActivity Sheet Empowerment Technologies Module 1Mykhaela Louize GumbanОценок пока нет
- MIL - Q1 - M4 - TYpes of MediaДокумент16 страницMIL - Q1 - M4 - TYpes of MediaGENEVIVE ALDEAОценок пока нет
- 15 The Disadvantages of ICTДокумент7 страниц15 The Disadvantages of ICTRussel LinondoОценок пока нет
- The Disadvantage of ICTДокумент7 страницThe Disadvantage of ICTMaja Julielle BillonesОценок пока нет
- The Disadvantages of ICTДокумент9 страницThe Disadvantages of ICTFlorenzo Miguel AclanОценок пока нет
- CV Kevin Ikhwan Muhammad Pt. Hasakona BinaciptaДокумент6 страницCV Kevin Ikhwan Muhammad Pt. Hasakona BinaciptaKevin MuhammadОценок пока нет
- Pakistan Machine Tool Factory Internship ReportДокумент14 страницPakistan Machine Tool Factory Internship ReportAtif MunirОценок пока нет
- Anti Banned HostДокумент1 276 страницAnti Banned HostVicky Kumar?skОценок пока нет
- Boeing 757 Normal Checklist: Power Up & Preliminary PreflightДокумент4 страницыBoeing 757 Normal Checklist: Power Up & Preliminary PreflightАлексей ЯрлыковОценок пока нет
- History Desktop PublishingДокумент16 страницHistory Desktop PublishingsanchezromanОценок пока нет
- Overhall Diferencial Mack PDFДокумент150 страницOverhall Diferencial Mack PDFmanuel fernandezОценок пока нет
- A. Irimia Diéguez 2023 - TPBДокумент23 страницыA. Irimia Diéguez 2023 - TPBakuntansi syariahОценок пока нет
- Background of UNITAR International UniversityДокумент3 страницыBackground of UNITAR International UniversityAin NadiaОценок пока нет
- BER-E222 PMДокумент8 страницBER-E222 PMItalo MendozaОценок пока нет
- Specification For Foamed Concrete: by K C Brady, G R A Watts and Ivi R JonesДокумент20 страницSpecification For Foamed Concrete: by K C Brady, G R A Watts and Ivi R JonesMaria Aiza Maniwang Calumba100% (1)
- SP25Y English PDFДокумент2 страницыSP25Y English PDFGarcia CruzОценок пока нет
- 24 - Counting of Bottles - Solution - ENGДокумент3 страницы24 - Counting of Bottles - Solution - ENGhaftu gideyОценок пока нет
- HS 30 eДокумент9 страницHS 30 eJayakrishnaОценок пока нет
- OPA237Документ21 страницаOPA237philprefОценок пока нет
- Learn PowerShell Core 6.0Документ800 страницLearn PowerShell Core 6.0Felippe Coelho100% (2)
- The Economic Essentials of Digital StrategyДокумент13 страницThe Economic Essentials of Digital StrategydhietakloseОценок пока нет
- Huawei RTN 980-950 QoS ActivationДокумент7 страницHuawei RTN 980-950 QoS ActivationVenkatesh t.k100% (2)
- Corea 2016 Cost HandbookДокумент70 страницCorea 2016 Cost HandbookEdutamОценок пока нет
- Reference Letter of DR Zaka EmadДокумент2 страницыReference Letter of DR Zaka EmadRMRE UETОценок пока нет
- 1St Flr. Reflected Ceiling Plan 2Nd Flr. Reflected Ceiling PlanДокумент1 страница1St Flr. Reflected Ceiling Plan 2Nd Flr. Reflected Ceiling PlanMac KYОценок пока нет
- TMB 60Документ2 страницыTMB 60oac08Оценок пока нет
- Steam Generator ManualДокумент25 страницSteam Generator Manualcolleen berganciaОценок пока нет
- Factors Affecting Grade 12 Students To Use Internet During Class HourДокумент39 страницFactors Affecting Grade 12 Students To Use Internet During Class HourJerric Brandon FalconiОценок пока нет
- LCD Interfacing With Microcontroller 8051Документ50 страницLCD Interfacing With Microcontroller 8051Darshan Vala100% (2)
- Azuma 2015 Metrologia 52 360Документ17 страницAzuma 2015 Metrologia 52 360Rudolf KiraljОценок пока нет
- Volvo Ec35D: Parts CatalogДокумент461 страницаVolvo Ec35D: Parts Cataloggiselle100% (1)
- Silo Over-Pressurization Prevention GuideДокумент30 страницSilo Over-Pressurization Prevention Guidemohamad izzuddin adnanОценок пока нет
- DIY Homemade Septic System PDFДокумент9 страницDIY Homemade Septic System PDFCebu CribsОценок пока нет